Solutions > Data Transfer Security
Cerberus FTP Server
Data Transfer Security
Strong transfer encryption, robust access security, comprehensive logging and streamlined compliance tools to support data transfer security and privacy requirements
It is one of a kind. 99% of searches done looking for “File Sharing” are cloud-based. This is not applicable for a lot of agencies that protect sensitive data that prefer or require data to remain on-premise. In addition, Cerberus FTP Server is scalable, clean-cut and simple for end users, and supports multiple sharing protocols.
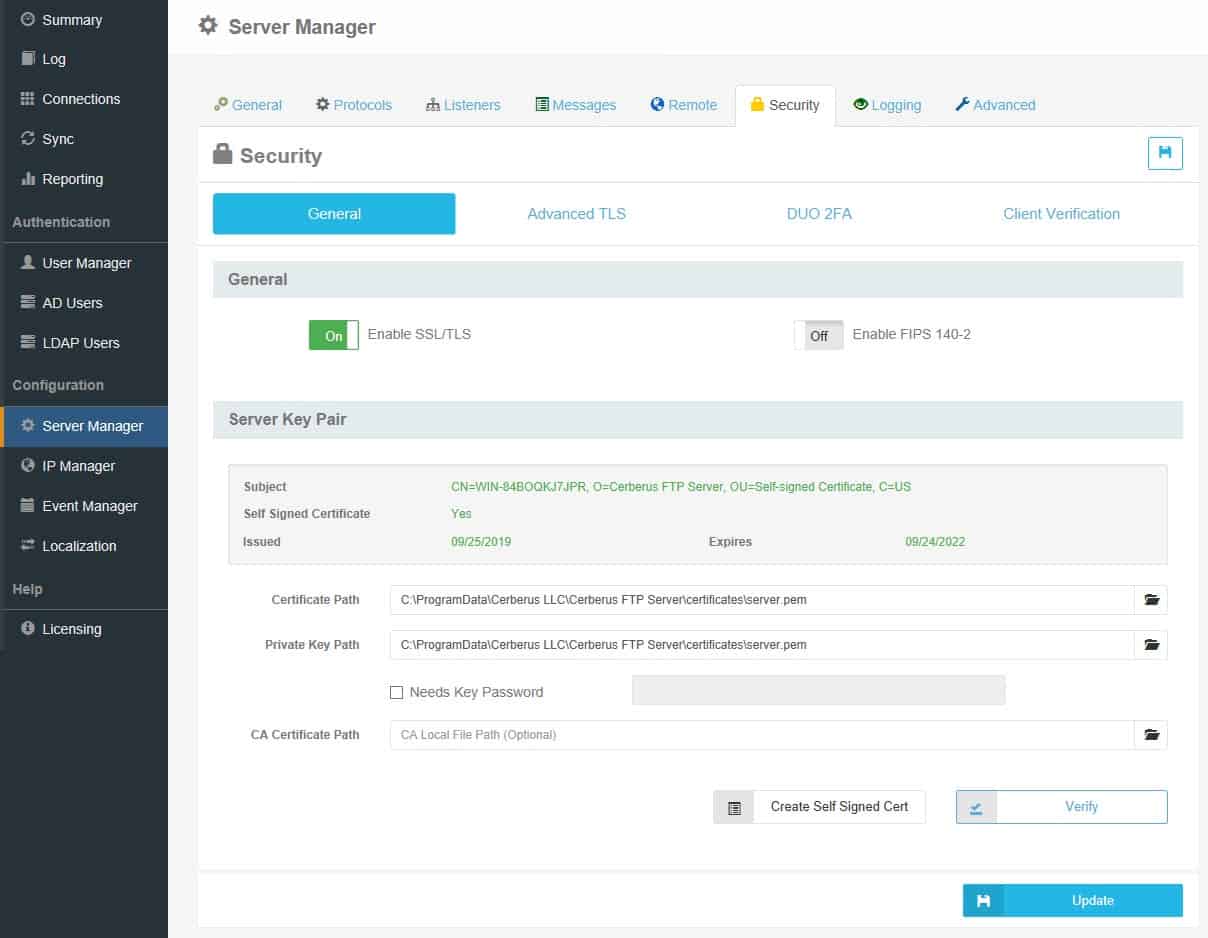
Data Transfer Security Over Any Protocol
Use the Server Manager to transfer via FTPS, SFTP, HTTPS, or SCP, with support for TLS 1.3, SSL cipher specification; RSA, DSA, and Elliptical Curve public and private keys; and Ephemeral Diffie-Hellman key exchange.
FIPS 140-3 Validated
Data transfer security certified to meet or exceed U.S. federal government data security standards.
File Transfer Integrity Checking
Using strong checksums based on SHA-512 or SHA-256 cryptographic hashes that can be configured for Encrypt-Then-MAC (ETM) processing.
Secure File Access
Cerberus FTP Server’s User Manager provides data transfer security through user- and protocol-based connection and login requirements; automatic account lockouts; password policies and change alerts; temporary user accounts; and the ability to block FXP and reserved ports for PASV connections.
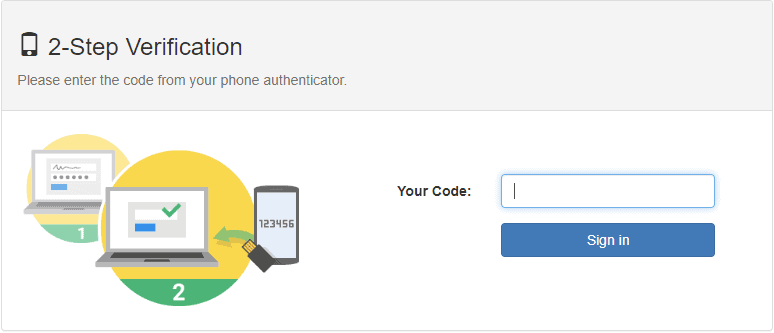
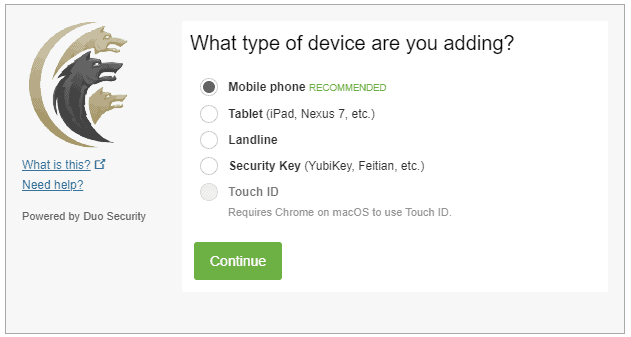
Multi-Factor Web Client Authentication
Using HOTP and DUO Security for both HTTP/S web client and web administration users.
SFTP/SCP Multi-Factor Authenticaion
Active Directory FTP Security Groups
Including Certificate Revocation Lists (CRLs).
Client Certificate Verification
Via several different configuration options, including our OpenSSL command line tool.
SSH2 Public Key Authentication
Available in Cerberus FTP Server Professional Edition and above via the User Manager.
IP Allow and Deny Lists
Through Cerberus FTP Server’s IP Manager, which includes auto- and geo-blocking to prevent DoS and brute force attacks.

Automatic Auditing & Logging
Cerberus FTP Server provides a complete view of your data transfer security at all times. Conduct full audits of all commands and file activity (including TLS/SSL cipher and bit strength per connection) while streamlining reporting with Syslog integration and rolling log files with configurable size limits.
Detailed Reporting
Report Manager generates detailed client activity audits based on user names, dates ranges, and file access.
SQL Database Capture
Cerberus FTP Server’s Enterprise Edition allows administrators to create detailed connection, login and file transfer reports with enhanced report filtering/ordering by file name, file time stamp, user, date, or host.
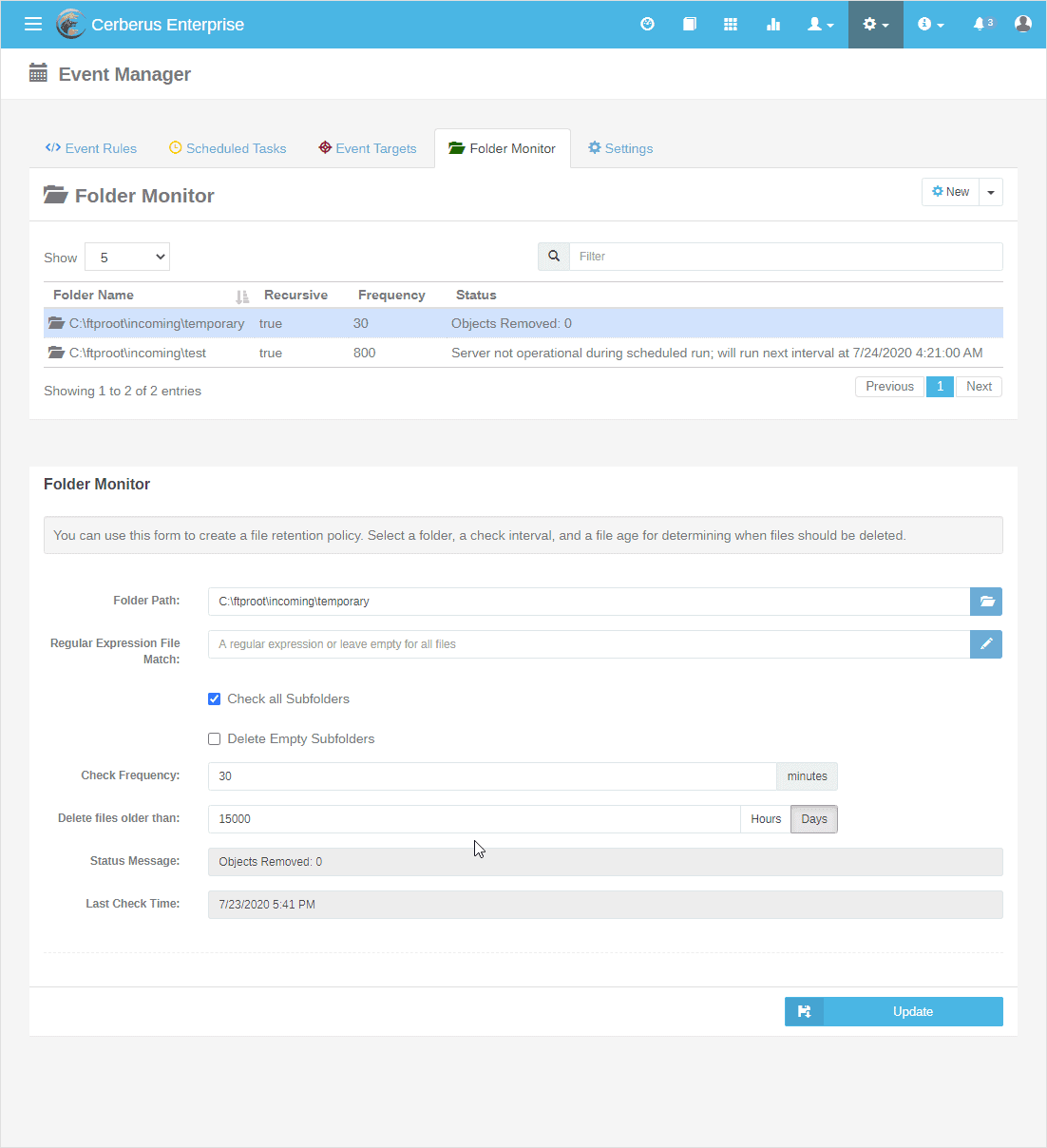
File Retention Policy Management
Cerberus FTP Server offers several tools to simplify data retention policies:
Folder Monitor
Configure automated file retention policies for all directories and sub-folders.
Advanced Policy Automation
Set up advanced policies, including alerts and batch file actions, using Enterprise Edition’s Event Manager.
Regulations Governing Data Transfer Security
In this section, we provide a list of regulations to help your IT administration understand the data transfer security requirements for your industry or jurisdiction.
General Data Protection Regulation - EU
Health Insurance Portability and Accountability Act (HIPAA) - USA
Major Requirements
- A covered entity must implement technical policies and procedures that allow only authorized persons to access electronic protected health information (e-PHI)
- A covered entity must implement hardware, software, and/or procedural mechanisms to record and examine access and other activity in information systems that contain or use e-PHI
- A covered entity must implement policies and procedures to ensure that e-PHI is not improperly altered or destroyed. Electronic measures must be put in place to confirm that e-PHI has not been improperly altered or destroyed
- A covered entity must implement technical security measures that guard against unauthorized access to e-PHI that is being transmitted over an electronic network
For More Information:
For more information:
Try Cerberus FTP Server free for 25 days
- Live US-based phone & email support
- Bulletproof reliability
- Built for complete data control
- Trouble-free enterprise deployment
Full Cerberus FTP Server Feature List
Protocols
FTP, FTP/S, SFTP, SCP, HTTP/S
Advanced Security
SSH, SSL, FIPS 140-3
MFT Automation
Event, Alert & Sync Tools
Environments
Windows Server, Cloud & Virtual
Access Protection
IP, User & Protocol Restriction Tools
Account Management
AD, LDAP, 2FA, SSO & More
Auditing and Reporting
File Access, User and Admin Logging
Administration Tools
API, Sync Manager, & Other Tools
HTTPS Web Portal
Browser-Based Transfer from Any Device
Monitoring & Testing
Automated Network, Load and Access Testing
Regulatory Compliance
Auditing, Retention, & Encryption Tools
Award-Winning Support
Phone, Email, & 24/7/365
Industry-Focused Solutions
Cerberus FTP Server supports a wide range of industry and professional needs. Enhance data security, streamline operations, and ensure compliance with regulations.
Uncompromising Commitment To Customer Satisfaction
G2

4.8 / 5
Capterra

4.8 / 5
CNET Download

4.8 / 5
Recognized as an industry-leading secure FTP server
Trusted by Companies Like Yours
Uncompromising Customer Satisfaction






Latest News
Cerberus FTP Server by Redwood version 2026.2: Enhancing the quality of life for admins and users
Cerberus by Redwood version 2026.2 focuses heavily on improving the daily experience for administrators and end users who live on our platform every single day. This release delivers essential enhancements and fixes designed specifically to remove friction and enhance...
Cerberus FTP Server 12.5 Introduces “Zip and Download” For Multiple Files
Save clicks and time with this new and efficiency-improving feature - download multiple files and folders by bundling them together in a single downloadable file. About the new feature Users have frequently requested a faster way to download multiple files and folders...
Zip/Unzip permission bypass vulnerability fixed in Cerberus FTP Server versions 11.0.3 and 10.0.18
Security Advisory Description Cerberus FTP Server Enterprise Edition prior to versions 11.0.3 and 10.0.18 are vulnerable to a permissions bypass when a user has zip/unzip permission. When zipping, users could zip files and folders that weren't visible to them; and...
Explore what Cerberus FTP Server can do for you
- 25 Day Free Trial
- No Credit Card Required
- Up and running in less than 15 mins