Solutions > Secure File Sharing for Law Firms
Cerberus FTP Server
Secure File Sharing for Law Firms
Strong encryption, security and compliance tools help law firms share files with absolute data confidentiality and protection
“Easy to use, simple to implement. End users can find their way around it without needing much if any training.”
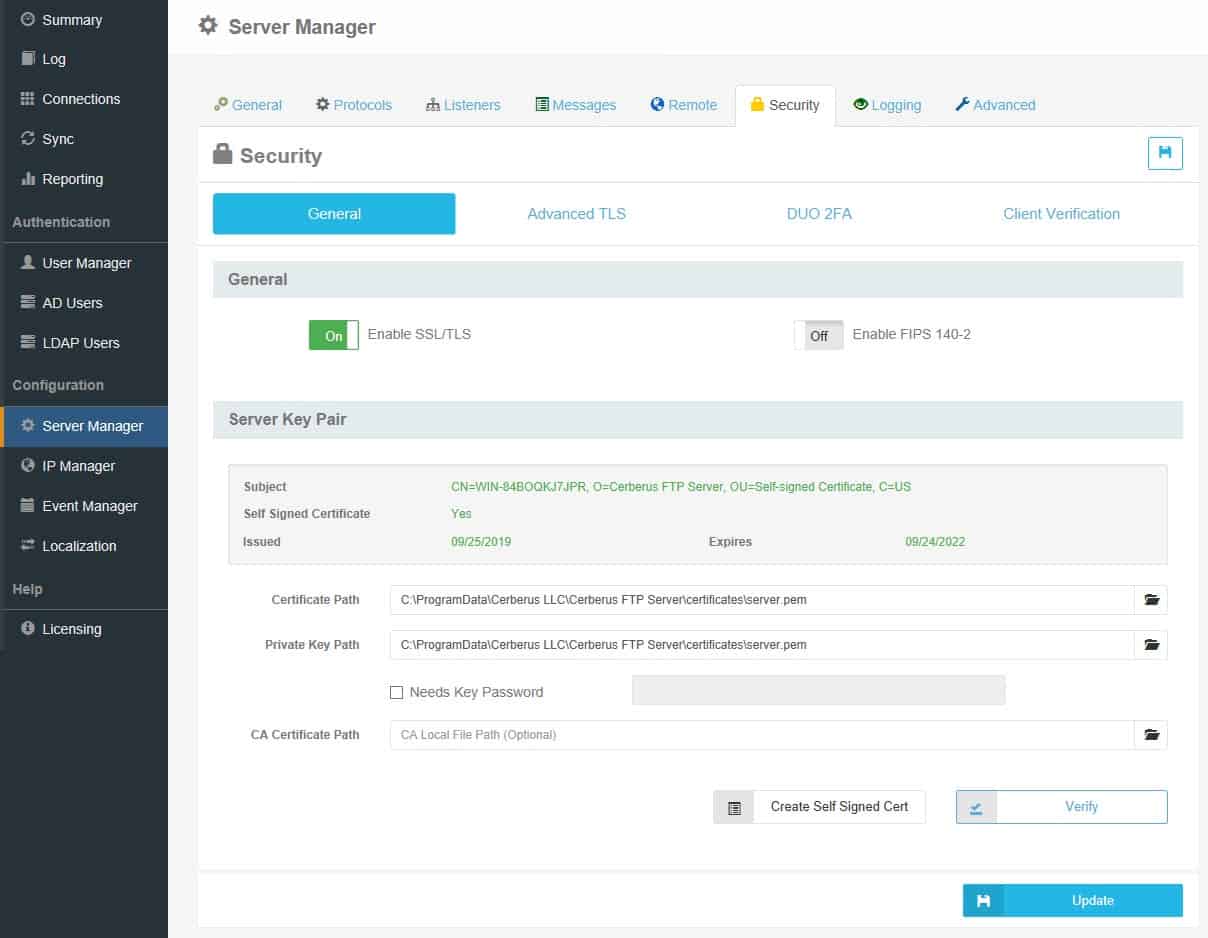
Encryption that Ensures Privacy
Ensure that only your intended parties are able to access your files with Cerberus FTP-Server’s enterprise-grade file transfer encryption for law firms.
Flexible Encryption Key Management
Cerberus FTP Server offers numerous key management tools, including SSH2 public key authentication; support for RSA, DSA, and Elliptical Curve public and private keys; and support for Ephemeral Diffie-Hellman key exchange.
Encrypted File Transfer
Easily Manage Compliance and Security
Cerberus FTP Server’s powerful tools support the most stringent internal compliance and security policies to ensure that files shared by your lawyers don’t fall into the wrong hands.
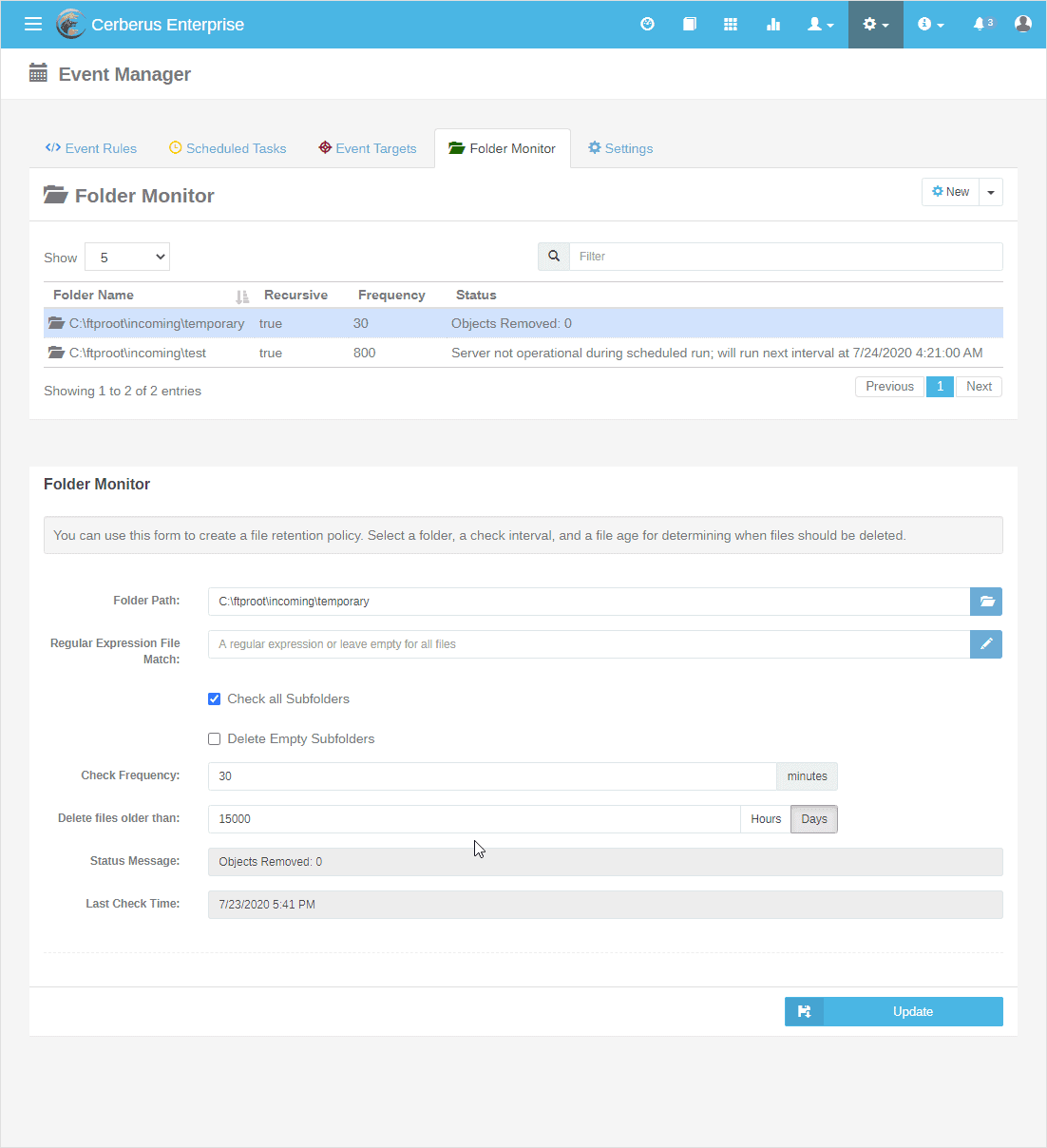
File Retention Policy
Our Folder Manager feature allows file and access deletion based on administrator criteria.
Activity Tracking
Report Manager provides full audit trails of when, where and how your law firm’s file transfer occured, along with transfer and connection statistics by user.
Eliminate Insecure Email File Transfer
Cerberus FTP Server’s ad-hoc file transfer option is the ideal file sharing tool for lawyers looking to provide unique, time-limited public links via HTTPS.
Authentication Security
Set up security groups in AD or LDAP integrations. Authenticate users with 2FA and client certificate validation. Ensure secure user access with password policy settings.
Active Directory Security Groups
Ensure data access policies are followed with Cerberus FTP Server’s AD security group integrations, which including certificate revocation lists (CRLs).
Requirements for Secure File Sharing at Law Firms
The legal industry largely self-regulates its cybersecurity policies in compliance with the jurisdiction or industry in which a firm may operate. This section provides an overview of the major industry requirements that apply to secure file sharing for law firms.
E.U. - Council of Bars and Law Societies of Europe (CCBE)
The E.U.’s General Data Protection Regulation provides the core framework for European file transfer security. However, the Council of Bars and Law Societies of Europe (CCBE) also provides guidance for law firms operating within the E.U.’s jurisdiction.
U.S. - American Bar Association
The ABA provides guidance for lawyers in Formal Opinion 477R*, which states “A lawyer should understand and use electronic security measures to safeguard client communications and information….if client information is of sufficient sensitivity, a lawyer should encrypt the transmission.”
U.S. - Legal Cloud Computing Association
The LCCA encourages its members and legal service providers to adopt the following data security practices:
- Standard 5: Encrypt all transmitted data
- Standard 8: Ensure that data retention policies are in effect to properly delete access to client data
- Standard 9: Use strong end user authentication
- Standard 11: Be able to track user activity within the firm’s system
- Standard 21: Have a disaster recovery plan in place
Learn more here: The Legal Cloud Computing Association’s Security Standards
Try Cerberus FTP Server free for 25 days
- Live US-based phone & email support
- Bulletproof reliability
- Built for complete data control
- Trouble-free enterprise deployment
Full Cerberus FTP Server Feature List
Protocols
FTP, FTP/S, SFTP, SCP, HTTP/S
Advanced Security
SSH, SSL, FIPS 140-3
MFT Automation
Event, Alert & Sync Tools
Environments
Windows Server, Cloud & Virtual
Access Protection
IP, User & Protocol Restriction Tools
Account Management
AD, LDAP, 2FA, SSO & More
Auditing and Reporting
File Access, User and Admin Logging
Administration Tools
API, Sync Manager, & Other Tools
HTTPS Web Portal
Browser-Based Transfer from Any Device
Monitoring & Testing
Automated Network, Load and Access Testing
Regulatory Compliance
Auditing, Retention, & Encryption Tools
Award-Winning Support
Phone, Email, & 24/7/365
Industry-Focused Solutions
Cerberus FTP Server supports a wide range of industry and professional needs. Enhance data security, streamline operations, and ensure compliance with regulations.
Uncompromising Commitment To Customer Satisfaction
G2

4.8 / 5
Capterra

4.8 / 5
CNET Download

4.8 / 5
Recognized as an industry-leading secure FTP server
Trusted by Companies Like Yours
Uncompromising Customer Satisfaction






Latest News
Understanding file transfer security risks
Secure file transfer has come a long way from the days of unencrypted FTP. And while today’s file transfer solutions like Cerberus FTP Server by Redwood provide excellent security and reliability, no protocol is perfect. So today, we’re reviewing the security risks of...
How will SFTP evolve in the future?
The Secure File Transfer Protocol (aka the SSH File Transfer Protocol, or SFTP) has become a foundational protocol of the internet since its invention in the late 1990s. And while its predecessor, FTP, will likely fade from usage in the near future, SFTP servers are...
What’s the Best File Transfer Method for Cisco Unified Communications Manager (CUCM) Backups and Firmware Updates?
SFTP servers are commonly used for updating and backing up devices and endpoints controlled by either Cisco Unified Computing System Manager (UCSM) or Cisco Unified Communications Manager (CUCM). And because of Cisco’s ubiquity in the market, the two most common...
Explore what Cerberus FTP Server can do for you
- 25 Day Free Trial
- No Credit Card Required
- Up and running in less than 15 mins