In Cerberus FTP Server 2024.1, we have added support for Duo Universal Prompt. For users who have Duo enabled, the traditional Duo Prompt enabled in previous versions of Cerberus will stop functioning on March 30, 2024; upgrading to the latest version is required for Duo to continue functioning as a second factor method.
If you are new to Duo and setting up your first application, you can skip to the upgrade notes and create a new application by clicking “Protect an Application” and selecting “Web SDK” towards the bottom of the list.
Traditional Prompt End of Support
On March 30, 2024, Duo will no longer support the traditional Duo Prompt; certain Duo editions will only be able to use the Universal prompt; there will be no Duo support provided for troubleshooting traditional prompt issues; the Web SDK v2 will no longer be supported.
As a current Duo administrator, your team should have received a notification to upgrade your Duo configuration. See the Duo Universal Prompt Update Guide for details if you have not completed this three step process.
Basically, if your application is of type “Auth API”, you need to complete the upgrade so that you have an application with the type “Web SDK” as shown in the screenshot below.
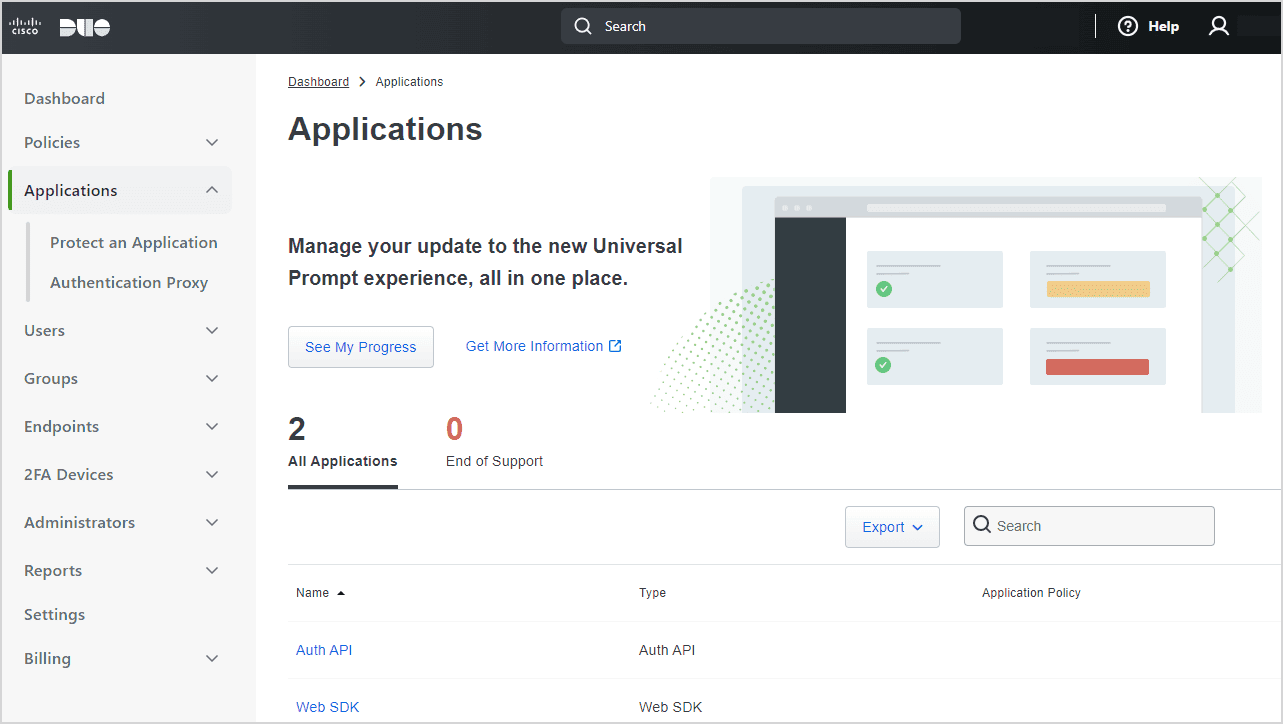
Duo Applications
Clicking on the Web SDK application and clicking the “See Update Progress” link in the Universal Prompt section will show you any tasks you need to complete as shown in the screenshot below.

Upgrading to Universal Prompt
Enabling Universal Prompt
Clicking on the “Web SDK” application will open the application settings as shown in the screenshot below.
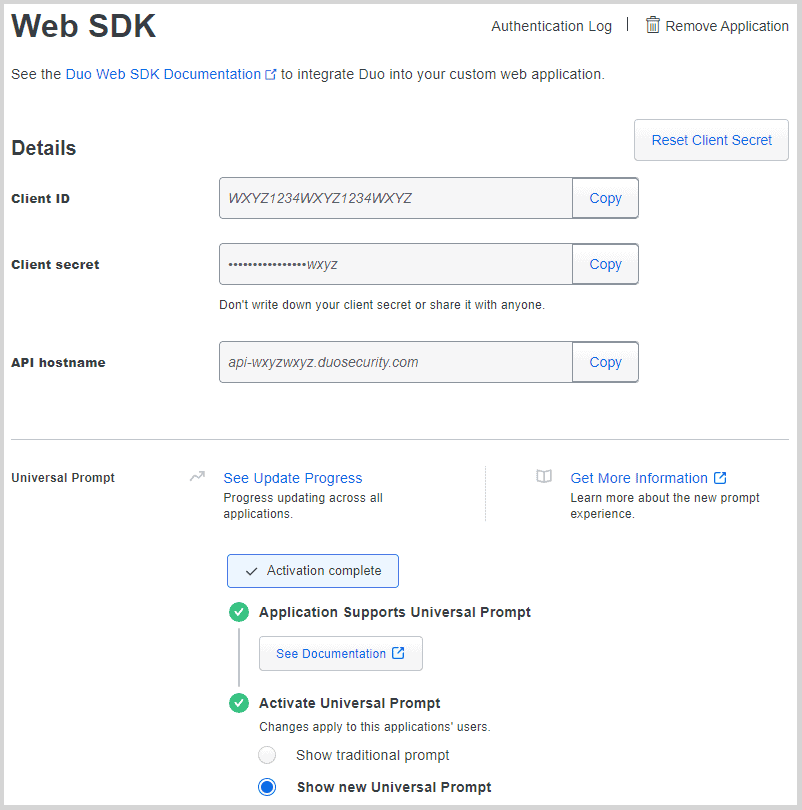
Web SDK Application
If this is a new or converted application, you will need to add the Client ID, client secret, and API hostname into Cerberus in Server Manager : Security : 2FA Duo Security Auth API section.
If you have selected manual enrollment, make sure you have at least one user setup in Duo Users, if auto-enrollment is enabled, then logging into Cerberus will take the user through the process.
When you’re ready, in Cerberus, select “Enable DUO 2FA Integration” and save.
Now login with a user that will be using Duo. If the user is required to use 2FA, then the enrollment process will automatically start; otherwise, go to Account and click on the “Enable 2 Factor” button. Click “Enable” in the popup. Complete the Duo process and login.
Once you have logged in at least one user, you can go back to the Duo administration page, select the Web SDK application and move from “Show traditional prompt” to “Show new Universal Prompt”.
Now users who login will be shown the new Universal Prompt and all the authentication options you have allowed in your Duo configuration.
Potential Issues
Previously Duo would work with IP address URLs like: https://127.0.0.1. With Duo Universal, you must now use fully qualified hostnames. Assuming DNS is properly configured, using https://localhost or https://mymachine.example.org would work. Specifically, Duo says in their API documentation:
Must be a well-formed with a valid HTTPS URL and port, using a hostname.Maximum length: 1024 characters.
Some Windows servers do not contain the “DigiCert SHA2 High Assurance Server CA” intermediate certificate used by duosecurity.com. When “Verify Remote Host Certificates” in Server Manager : Security : Server Verification is on, Cerberus will reject connecting to Duo if it cannot verify the full certificate chain.
You can download the certificate from DigiCert Trusted Root Authority Certificates in the “Other intermediate certificates” section. The “Download DER/CRT” link retrieves a certificate that works well with Windows’ Certificate Manager.
Open the certificate, select “Install Certificate…”, select “Local Machine,” click “Next”, then select “Automatically select the certificate store based on the type of certificate”, click “Next”, and then click “Finish”. The importer should report “The import was successful.”
Availability
These are just some of the new features that are available in Cerberus FTP Server 2024.1 editions. To learn more about all the new features in Cerberus FTP Server 2024.1, check out our release notes here.
We look forward to hearing how our customers use this updated integration and how any improvements would help you set up and maintain Two Factor authentication. As always, we would love to hear your feedback.