In Cerberus FTP Server 13.1, we have moved Certificate Signing Request (CSR) functionality from a Windows dialog into the web based user interface. The associated menu item under Tools has also been removed. This means that administrators can now access this functionality remotely as they have been able to do with Self-Signed Certificates.
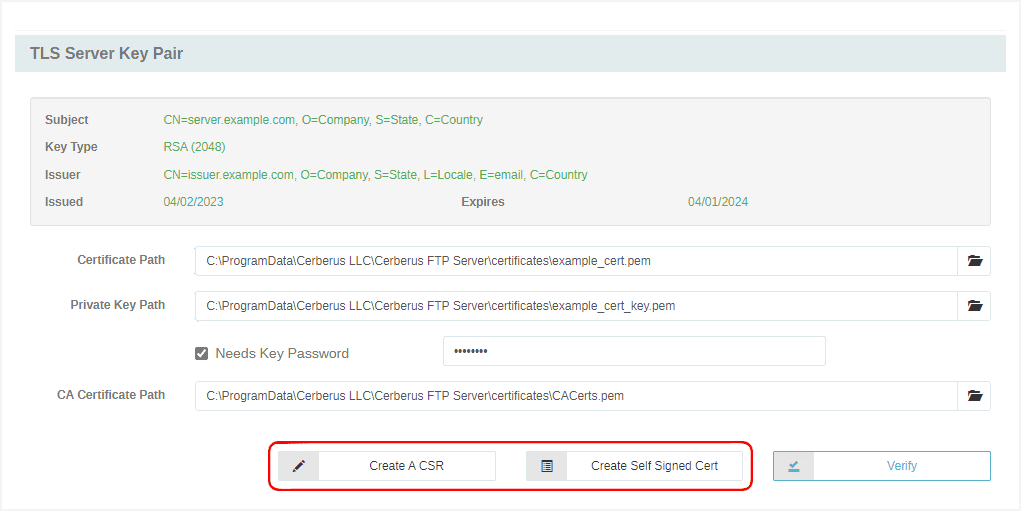
TLS Server Key Pair
Both these features can be accessed from the Server Manager / Security / General panel in the TLS Server Key Pair section as shown in the screenshot below.
Certificate Signing Request (CSR)
As with the Self-Signed Certificate form, the new CSR form allows an administrator to fill in the certificate details (all fields except email require a value). The new form is shown below:
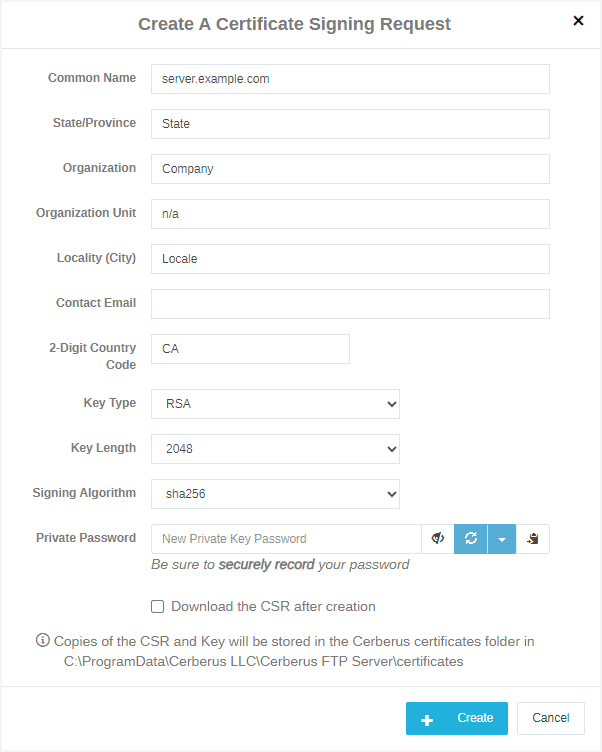
CSR form
The new CSR form offers additional Key Type algorithms – options include: RSA, DSA, ECDSA, EdDSA 25519, and EdDSA 448.
The Key Length options depend on which Key Type is selected; where supported, various lengths can be selected based on the organization’s security requirements. The EdDSA options have a fixed length and therefore have no selection option.
The Signing Algorithm options have also been updated. Depending on the Key Type, a number of options are available; older options have been labeled with the “(Legacy)” tag to indicate that extra care should be taken if these options are selected. The EdDSA options have a fixed length and therefore have no selection option.
Administrators can also set a password on the created Private key. This value is not stored by Cerberus at this stage; Administrators should securely store the password as they do other passwords as it cannot be recovered if forgotten. Once the Certificate Signing Authority signs the CSR and returns a valid certificate, the password will be needed to use the certificate in Cerberus.
Finally, administrators can check the “Download the CSR after creation” to automatically get a copy of the CSR on their local machine. A copy is always stored on the server as well and that location is listed on the form.
Self-Signed Certificates
The Self-Signed Certificates form has also been updated. As with the CSR form, new Key Type options have been added, along with applicable Key Length and Signing Algorithm values.
Similarly to the CSR, Self-Signed Certificates can now have a password on the generated Private key. If set, this password should be securely stored outside Cerberus in case it is needed in the future.
A new option “Enable as your server TLS Certificate immediately” allows setting Cerberus’ TLS Certificate to the newly created Self-Signed Certificate.
The updated Self-Signed Certificate form is shown below:
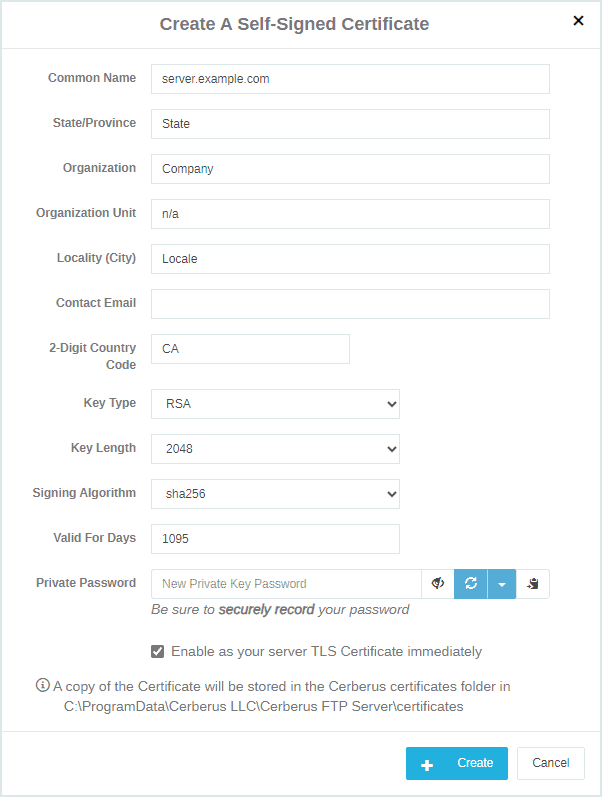
Self-Signed Certificate form
Notes
The Edwards-curve Digital Signature Algorithms (EdDSA) are fairly new and not widely supported yet by Certificate Signing Authorities; we expect these algorithms to become more common as time goes on.
In addition EdDSA is currently not allowed in FIPS mode. We expect this limitation to be removed once OpenSSL transitions to FIPS 140-3 validation which is based on FIPS 186-5 and SP 800-186. OpenSSL 3.1 FIPS 140-3 validation is currently in Implementation Under Test (IUT) as of Feb 2, 2023 and most likely won’t be available until the second quarter of 2024 at the earliest.
Availability
These are just some of the new features that are now available in Cerberus FTP Server 13.1 editions. To learn more about all of the new features in Cerberus FTP Server 13.1, check out our release notes here.
We look forward to hearing how our customers use these features and how any additional improvements would help you create and maintain Public Shares. As always, we would love to hear your feedback.