Security Advisory Description
Cerberus FTP Server Enterprise and Professional versions prior to 11.2.5 and 10.0.26 are vulnerable to an extension blocking bypass over the SCP protocol.
Scope
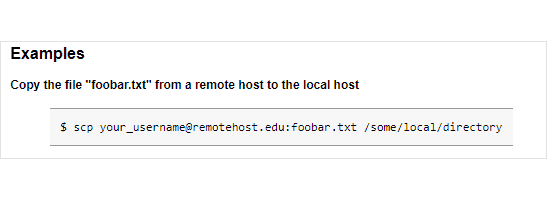
- This vulnerability impacts Cerberus FTP Server Enterprise and Cerberus FTP Server Professional deployments using SFTP listeners with the SCP protocol enabled.
- Other editions of Cerberus are not affected, as the SFTP protocol is only a feature of the Enterprise and Professional editions.
- Other transfer protocols, such as SFTP, FTP, FTPS, and HTTP(S) are unaffected.
Known Affected Versions
- 11.0 releases prior to 11.2.5
- 10.0 releases prior to 10.0.26
- 9.0 and older are out of support and no longer receiving updates. It is unknown whether issues in this advisory affect them.
Mitigation
This issue is addressed in version 11.2.5 and 10.0.26. Cerberus Administrators are encouraged to upgrade to one of these versions or higher as soon as possible.
Until upgrade is complete, Cerberus administrators may mitigate by disabling the SCP protocol on individual listeners if extension blocking is being used.
Credit
This vulnerability was discovered and reported by one of our valued customers. Special thanks for their efforts.